It was December 3, 1992. That’s the date that Neil Papworth sent the world’s first text message. More than 26 years later, SMS has grown into a powerful marketing and communication tool.
Today, trillions of SMS text messages connect billions of people and benefits millions of businesses and marketers immensely. SMS helps businesses generate outsized positive ROI.
In this article, we’ll review the most recent SMS usage statistics. Be warned! These stats might compel you to take your SMS marketing seriously.
Global SMS and Usage Statistics
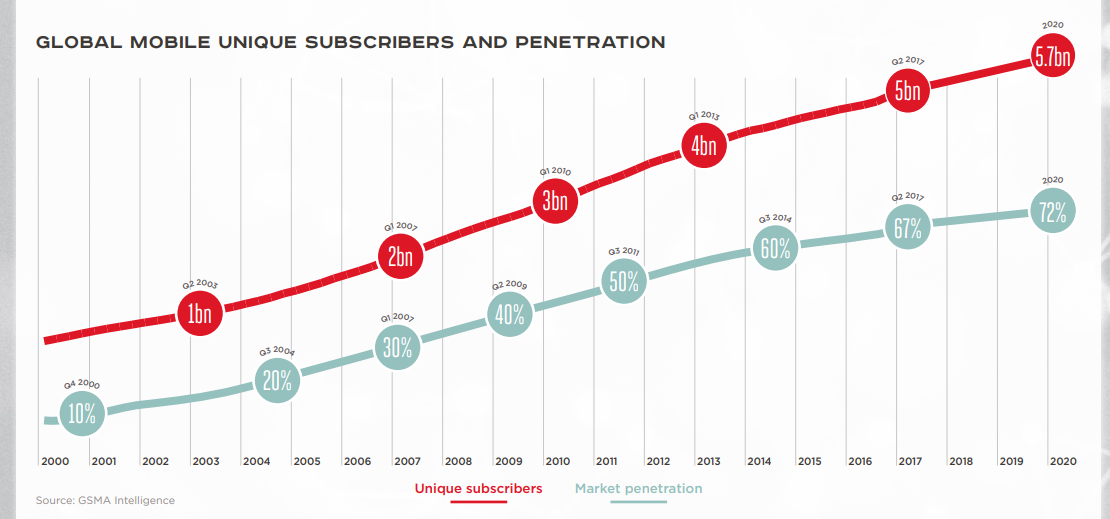
Image Credit: GSMA Intelligence
The number of mobile users is increasing and will continue to soar. In a GSMA report, mobile users will go from five billion users in 2019 to 5.7 billion in 2020. This growth will increase market penetration of mobile phones from 67 percent to 72 percent in that period. Hence, an increase in the use of SMS.
The GSMA statistics support Statista’s predictions that smartphone users will grow from 3.2 billion to 3.8 billion from 2019 to 2021. Another Statista report posits the number of mobile subscribers globally will reach 7.33 billion in 2023.
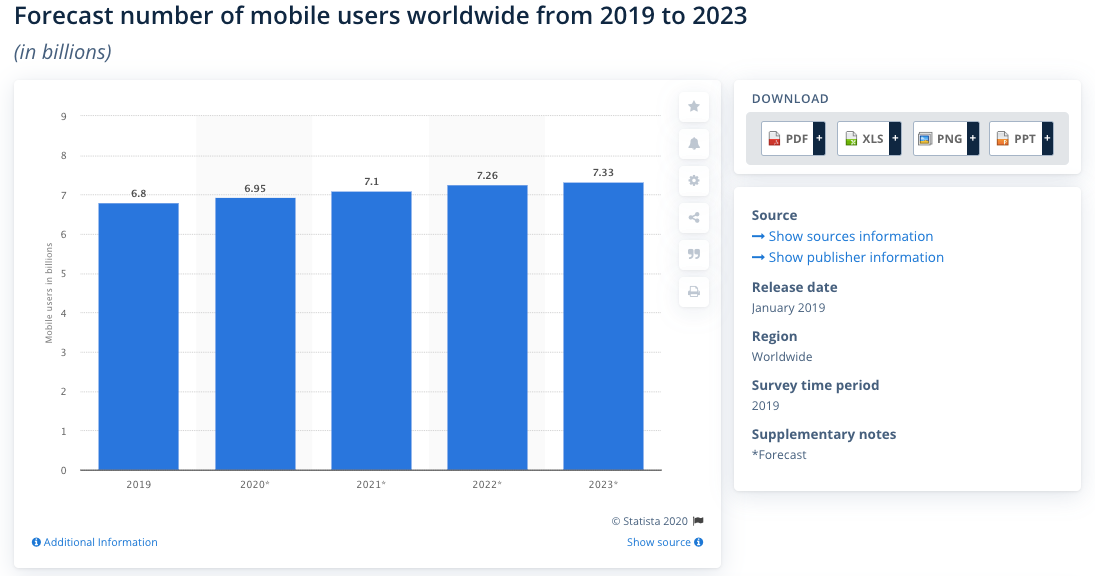
Screenshot from Statista
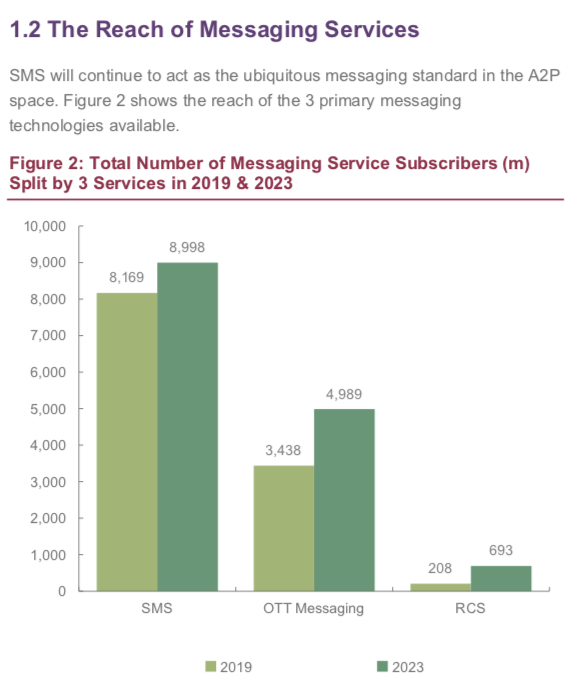
The growing number of mobile devices means SMS remains a viable communication platform.
In America, over 272 million people own smartphones. And they collectively check their phones tens of billions of times every day; an average person picks up their phone 58 times a day.
Let us look at some of the global SMS and usage statistics.
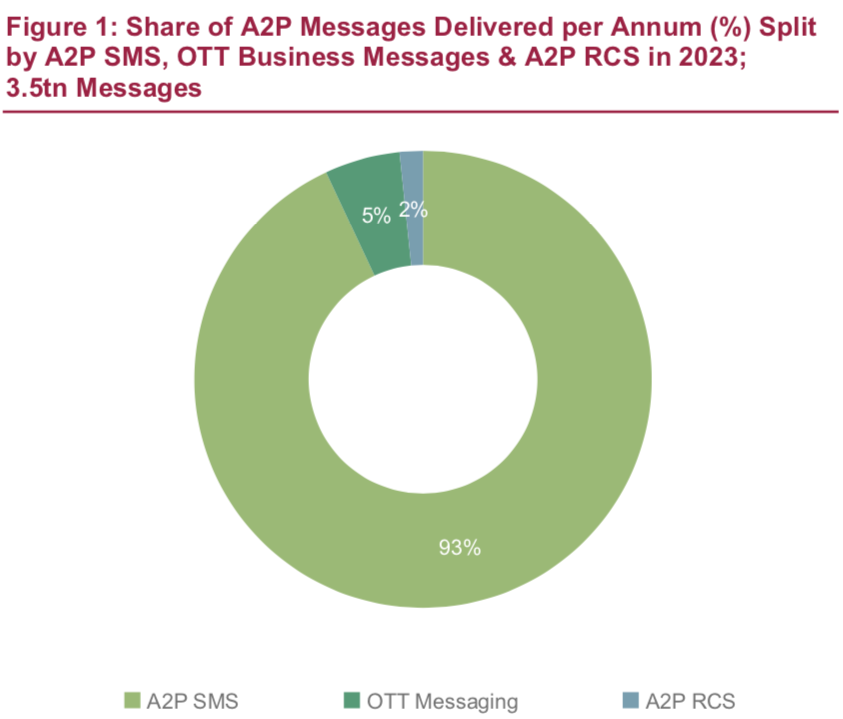
- In 2024, the global application to person (A2P) SMS API market will reach $245.9 million based on a CAGR of 4.1 percent from 2017 to 2024. However, the A2P SMS market will grow at a CAGR of 4.2 to reach a valuation of $86.53 billion in 2025.
- The A2P SMS market is stronger in the USA, growing at 6.2 percent to reach a valuation of $31.7 billion in 2022.
- Phone users read over 90 percent of text messages within three minutes of receipt.
SMS Marketing Statistics for Businesses

Screenshot from Ericsson
According to Ericsson, the number of mobile subscriptions in 2020 will exceed eight billion. Smartphones and feature phones will contribute to 73 percent and 23.4 percent of that growth, respectively.
Let’s explore the conversion and response rates of SMS.
- The average response time for a text message is 90 seconds while email has an average response time of two days.
- According to Finances Online, 90 percent of people in the US prefer to receive SMS over calls.
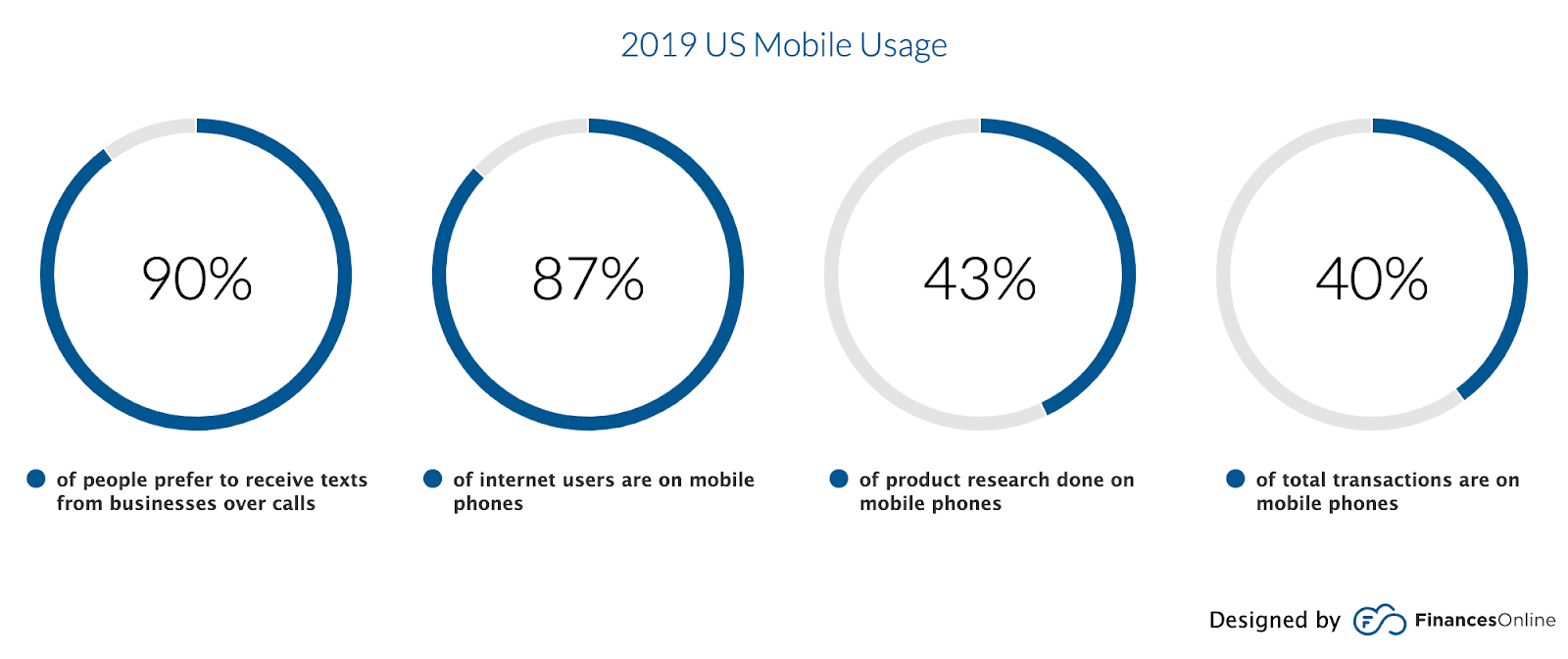
Screenshot from Finances Online
- Retailers that use promotional SMS for their CRM initiatives enjoy a 23.3 percent conversion rate.
- Compared to calls, 64 percent of customers prefer using two-way text messages when interacting with customer service. Most of these customers are younger people and they cite efficiency and convenience as their top reasons for preferring text messages.
- About 75 percent of customers enjoy receiving special offers by text message. Messages sent this way convert at 9.18 percent, which is several times higher than the 0.9 percent and 1.91 percent of Facebook and Google Ads, respectively.
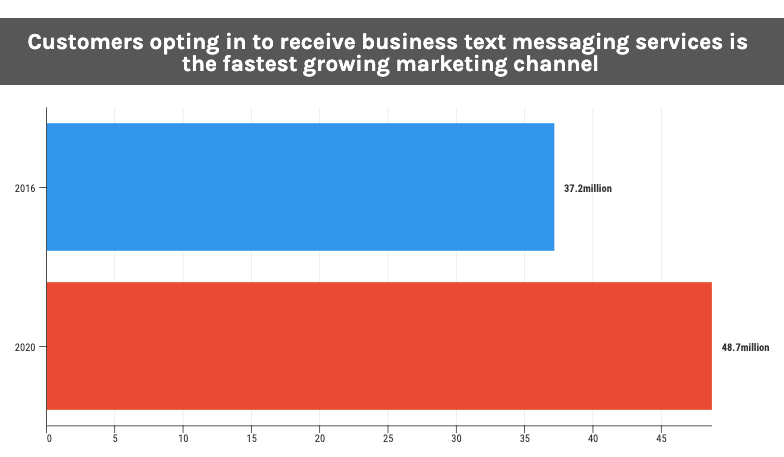
Image Created by Nicholas Godwin for SMSEagle.eu
- The fastest growing marketing channel is customers opting in to receive business text messaging services. In 2016, 37.2 million customers used this channel, in 2020 48.7 million customers in the US are choosing the channel.
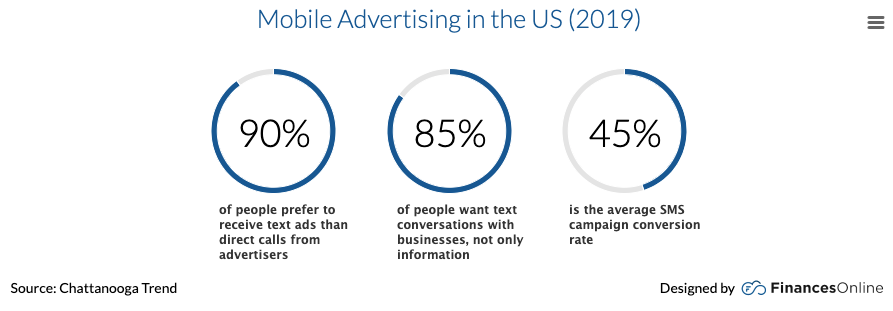
- In 2019, businesses spent $165.7 billion on mobile ads. In that year, 90 percent of US consumers indicated that they prefer to receive text ads.
- In 2019, the conversion rate of SMS campaigns stand at 45 percent.
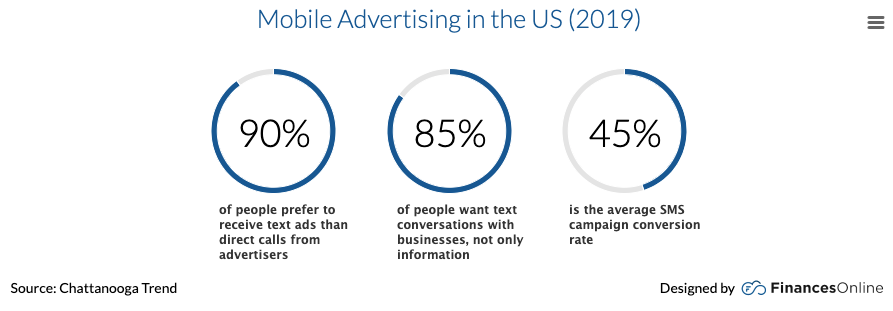
Screenshot from Finances Online
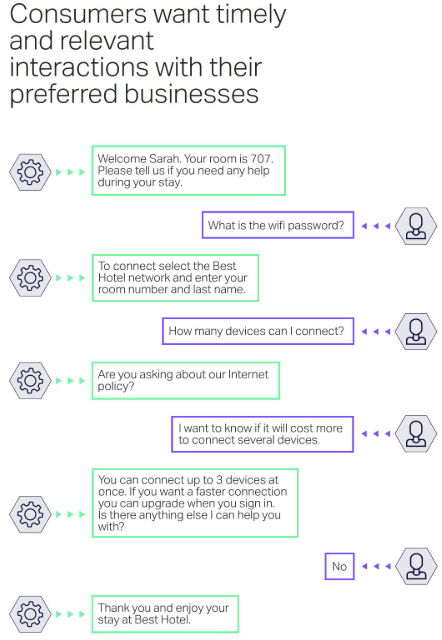
- Eighty-five percent of consumers and buyers want to go beyond receiving just information from businesses, they want to hold text conversions with these businesses.
- SMS open rate stands at 98 percent because receivers must read them before they delete them. Whereas, open rates for Facebook posts, email messages, and Tweets stand at 12 percent, 20 percent, and 29 percent, respectively.
- HubSpot reports that the average click through rate of URLs in text messages is 19 percent, meanwhile, email stands at 4.2 percent.
Marketing SMS Usage Statistics
Screenshot from GlobalWebIndex
- According to a 2019 Social Flagship report by GlobalWebIndex, 48 percent of internet users share content with their peers through text messages. Only 37 percent of users share information via email.
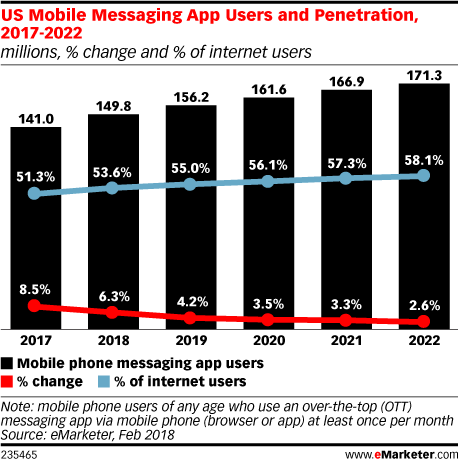
Screenshot from eMarketer
- The US mobile messaging app usage, including SMS app usage, will go from 161.6 million users in 2020 to hit 171.3 million users in 2022. This growth will go from 56.1 percent of the US population to 58.1 percent of US users.
- SMS Comparison further reveals that SMS has a higher clickthrough rate (CTR) when compared to other marketing like Facebook and Google AdWords. The Click-through rate for SMS stands at 9.18 percent, while Facebook and Google AdWords have a CTR of 0.90 percent and 1.91 percent, respectively.

Screenshot from OpenMarket
Sixty-two percent of buyers are not getting SMS notifications from retailers. In Travel and Hospitality, 75 percent of travellers and vacationers are not receiving any SMS communication from train operators, hotels, and airlines.
- According to SMS Comparison, nine out of ten customers will prefer to communicate with companies via text message. That stat applies to one-way communication by alerts, reminders, and notifications, or two-way communications.

Screenshot from Finances Online
- Mobile marketing, including SMS marketing, is driving more purchases for businesses in 2020. Businesses in these three industries are seeing the most increase in sales due to mobile marketing: 54 percent of restaurants, 40 percent of apparels and beauty, and 36 percent of electronics.
- According to Rebrandly, using branded links on your SMS campaigns will increase clickthrough rate by 39 percent and boost brand visibility.
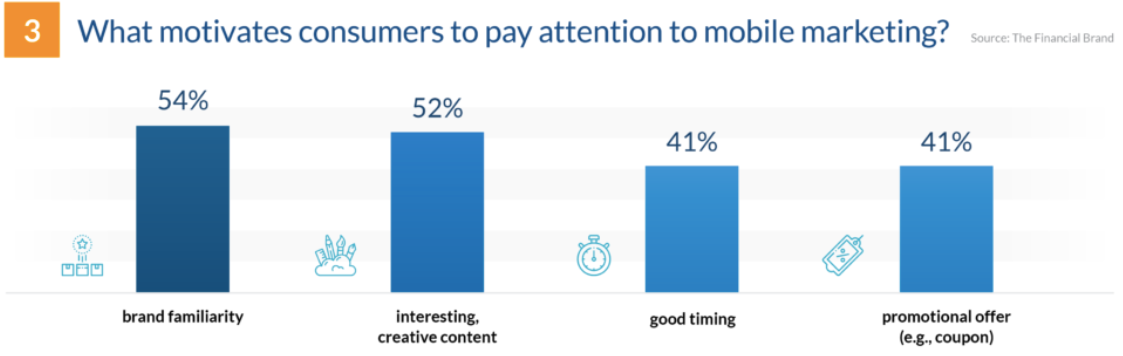
- The top four reasons why consumers pay attention to a marketing message in their mobile phone are: brand familiarly at 54 percent, content that’s interesting and creative at 52 percent, excellent timing at 41 percent, and promotional offers such as coupons at 41 percent.
Screenshot from Finances Online
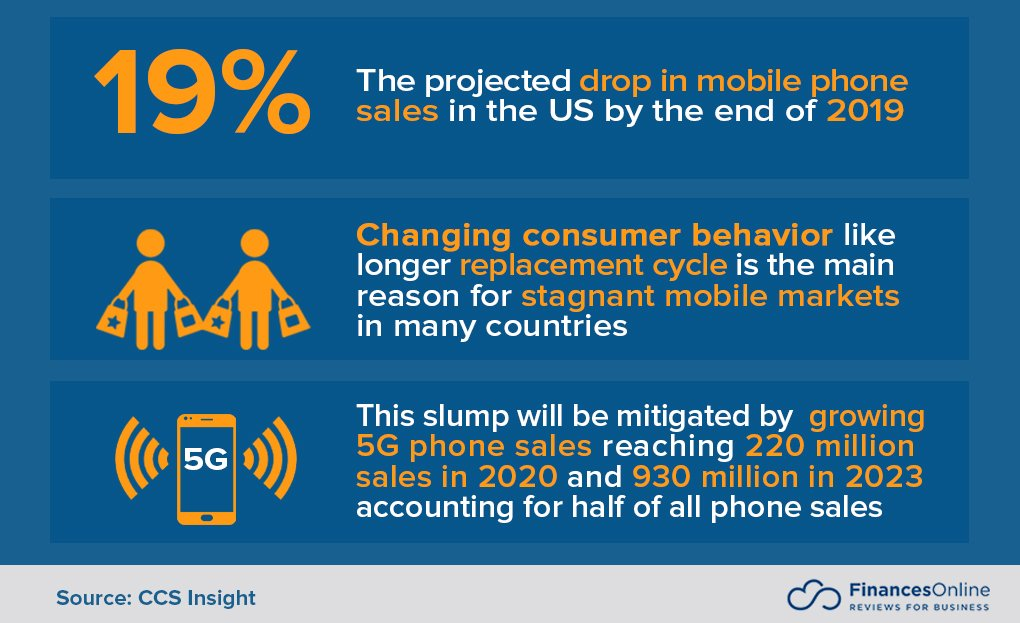
- By end-of-year 2019 the mobile phone sales market would witness a 19 percent drop because of longer phone replacement cycles.
Screenshot from Finances Online
- Researchers expect to see 49 million consumers opting to receive marketing messages from brands in 2020. Following the COVID-19 outbreak, Gartner says that SMS will become vital for businesses that want to keep touch with their audiences and customers at this time.
SMS Statistics from the Financial Service Industry

Mobile SMS banking has become a dominant trend
- According to the Business Insider Intelligence Mobile Banking Competitive Edge study by Business Insider, 89 percent of customers say they utilize mobile banking services.
- According to Coherent Marketing Insights, the transactional SMS market share will reach 47.4 percent by 2027.
What Does the Future Hold for SMS and SMS Marketing?
The SMS industry will continue to witness an upward swing. Future projections have shown that recent advancements in technology will shape consumers’ behavior and how businesses utilize SMS.
Screenshot from Juniper Research
Let’s take a look at some of the predictions.
- According to the Coherent Marketing Insights, the global bulk SMS marketing industry will hit a CAGR of 7.4 percent between 2019-2027.
- Juniper Research estimated that the number of business text messages in 2020 would reach 3.5 trillion messages from the 2.5 trillion messages in 2019.
Screenshot from Juniper Research
- Given the high engagement rates of SMS marketing and the intelligent automation capabilities of chatbots, experts expect that SMS chatbots will continue to grow for the foreseeable future.
Screenshot from OpenMarket
- From 2019 to 2027 the global market for bulk SMS marketing service will grow at a CAGR of 7.2 percent.
Final Words
From the usage statistics we have outlined here, it’s clear that the future of SMS is promising.
SMS remains the most underutilized, yet most engaging marketing and communication channel. And it’ll continue to witness adoption across multiple industries including financial services, healthcare, hospitality, transportation, and more.
With a massive open rate of 98 percent, SMS has the potential to deliver significant value for businesses. As a marketer, SMS communications means your customers will most likely read your message.
Furthermore, SMS marketing can help businesses boost customer reach. They can improve customer engagement and increase revenues. Businesses that engage in SMS marketing will continue to enjoy these enormous benefits if they employ the right strategies.
The beautiful thing about SMS is that it is cost-effective and can form an essential part of your integrated marketing strategy. You should go ahead and invest in SMS. I’m sure you will be glad you did.